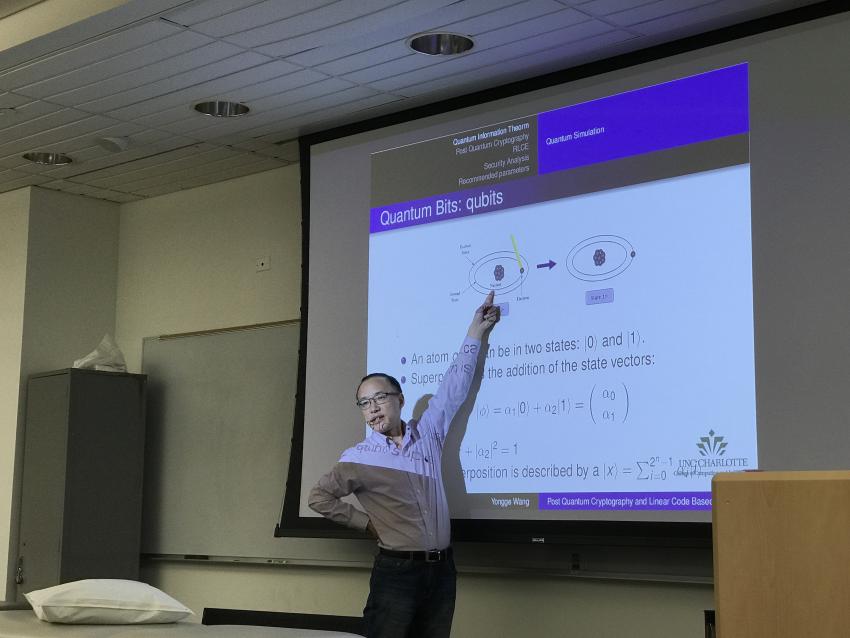
UNC Professor Dr. Wang Discusses Post-Quantum and Code Based Cryptography
Dr-Yongge-Wang-post-quantum-cryptography
Computer Science and Math Department hosted Dr. Yongge Wang, professor in the School of Information Systems at University of North Carolina Charlotte, where he discussed his work in cryptography and cryptographic scheme resistancy to quantum computer attacks.
Dr. Wang introduced quantum computing and its applications before he discussed his recent proposal on Random Linear Code based Encryption scheme (RLCE) to the National Institute of Standards and Technology (NIST). An industry on the rise, Quantum Computing will significantly speed up mathematical computations, leading to scientific discoveries in sciences, predictive analytics, and computational complexity. NIST has initiated the plan to design new quantum resistant public key cryptography standards, which Dr. Wang hopes to engage with through the RLCE proposal. He talked about the RLCE scheme using Generalized Reed-Solomon codes to analyze and strengthen the security parameters in order to be resistant to quantum computer attacks.
Dr. Wang is a well-known cryptographer and a developer of a cryptographic scheme resistant to quantum computer attacks. He has published over 100 peer-reviewed scientific papers on the foundation of mathematics, algorithm analysis, computational complexity theory, cryptology (encryption, decryption, and cryptanalysis), fault-tolerant computation, dependable distributed computation, infrastructure protection, secure communications, computer and network security, cloud security, information theory, and post quantum cryptography.
Dr. Wang has extensive experience in technology transfer and his work has had long-term impact on the information technology industry. Previous to UNC Charlotte, Dr. Wang worked at Certicom (now a division of BlackBerry Limited) as a cryptographic mathematician specializing in efficient cryptographic techniques for wireless communications. He is the inventor of Remote Password Authentication protocol SRP5, as well as the inventor of the Identity Based Key Agreement protocol. Dr. Wang has also worked with Cisco researchers and American Gas Association researchers to design security protocols for the SCADA industry.


